What's Happening @ FirstLight

How do you communicate in an emergency?
Blog
Today’s Reality In an age of instant communication and multiple devices, it’s easy to assume that notifying individuals during an emergency would be straightforward. After…

The FirstLight Difference
Blog
Ten Reasons Why the FirstLight Channel Program Means Success for You

Unveiling the Future of Networking: Understanding SASE (Secure Access Service Edge)
Blog
In an era defined by digital transformation, the way organizations approach networking and security is evolving rapidly. One of the groundbreaking innovations in this space…

Bell and FirstLight to offer new high-speed routes with triple redundancy between Secaucus, NJ, Toronto, and Montréal
Press Releases

FirstLight Enhances Its C-Suite with Two Industry Veterans
Press Releases
FirstLight augments its executive team with the appointment of Mike Constantino as Chief Operating Officer and Lorenzo Leuzzi as Chief Revenue Officer Albany, NY –…

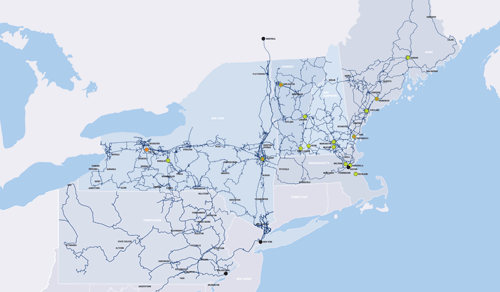
Aqua Comms Selects FirstLight for Unique Fiber Routes in the Northeast
Press Releases
Leading provider of global subsea connectivity services selects FirstLight to help diversely connect their transatlantic routes Albany, NY – August 3, 2023 – FirstLight, a…
FirstLight Wins Four Visionary Spotlight Awards
Press Releases
ChannelVision Magazine honors FirstLight for its “innovative solutions and emerging technologies” Albany, NY – July 12, 2023 – FirstLight, a leading provider of digital infrastructure…

New Area Code Coming to Western New York
Press Releases
The new 624 area code will be an overlay to the existing 716 area code Albany, NY – July 11, 2023 – FirstLight, a leading…

FirstLight Appoints Peter Zarrella as CFO
Press Releases
Seasoned Executive brings a wealth of experience and expertise in financial management, strategic planning as well as driving empowerment at all levels of an organization…

Wirebelt Company of America Chooses FirstLight to Support its New, Energy Efficient Manufacturing Facility
Press Releases
Metal conveyor belt manufacturing company selects FirstLight for its reliable, secure, and compliant data center services, Internet and dark fiber connectivity Albany, NY – May…

A Beginner’s Guide to Disaster Recovery as a Service
Blog
In today’s connected world, downtime is not an option.

FirstLight Fiber, Inc. Names Jason Campbell as Chief Executive Officer
Press Releases
Albany, NY – April 6, 2023 – FirstLight, a leading provider of fiber-optic data, Internet, data center, cloud, unified communications, and managed services to enterprise…

FirstLight Continues Fiber Network Expansion in Hebron, Sumner
Press Releases
Rural Maine communities to benefit from high-speed Internet Albany, NY – April 4, 2023 – FirstLight, a leading provider of digital infrastructure services to enterprise…

The 2023 Hype Alphabet Soup
Blog
With 2023 in full swing, tech leaders everywhere might be feeling stretched thin. Caught between strategic activities that set the guideposts for your team and…
New 329 Area Code Coming to the 845 Region in New York
Press Releases
New assigned area codes begin March 24th, 2023 Albany, NY – February 1, 2023 – FirstLight, a leading provider of digital infrastructure services to enterprise…

FirstLight Receives 2022 Backup and Disaster Recovery Award from Cloud Computing Magazine
General News
Ransomware Protection, Data Backup and Disaster Recovery as a Service Honored for Enhancing Organizational Security Albany, NY – January 30, 2023 – FirstLight, a leading…

FirstLight Announces Expansion of Residential Broadband in Maine
Press Releases
This investment helps to bridge the digital divide in unserved and underserved areas throughout the state Albany, NY – December 7, 2022 – FirstLight, a…

Performance-Grade Ethernet Explained
General News
As enterprise leaders work to create more seamless connections among office locations, data centers and cloud applications, they are increasingly choosing private connections like Ethernet.…

The Divide Podcast: How FirstLight is connecting communities with middle-mile fiber
General News
This week: FirstLight Fiber’s Maura Mahoney, Chief Marketing Officer, and Patrick Coughlin, Chief Development Officer, talk about tackling the digital divide through fiber ‘onramps and…
FirstLight to Exceed 1,700 Route Miles in New York in 2022
Press Releases
With over twelve hundred route miles already constructed this year, FirstLight remains committed to expanding in the Empire State Albany, NY – October 25, 2022…

How do you communicate in an emergency?
Blog
Today’s Reality In an age of instant communication and multiple devices, it’s easy to assume that notifying individuals during an emergency would be straightforward. After…

The FirstLight Difference
Blog
Ten Reasons Why the FirstLight Channel Program Means Success for You

Unveiling the Future of Networking: Understanding SASE (Secure Access Service Edge)
Blog
In an era defined by digital transformation, the way organizations approach networking and security is evolving rapidly. One of the groundbreaking innovations in this space…

Bell and FirstLight to offer new high-speed routes with triple redundancy between Secaucus, NJ, Toronto, and Montréal
Press Releases

FirstLight Enhances Its C-Suite with Two Industry Veterans
Press Releases
FirstLight augments its executive team with the appointment of Mike Constantino as Chief Operating Officer and Lorenzo Leuzzi as Chief Revenue Officer Albany, NY –…

Aqua Comms Selects FirstLight for Unique Fiber Routes in the Northeast
Press Releases
Leading provider of global subsea connectivity services selects FirstLight to help diversely connect their transatlantic routes Albany, NY – August 3, 2023 – FirstLight, a…
FirstLight Wins Four Visionary Spotlight Awards
Press Releases
ChannelVision Magazine honors FirstLight for its “innovative solutions and emerging technologies” Albany, NY – July 12, 2023 – FirstLight, a leading provider of digital infrastructure…

New Area Code Coming to Western New York
Press Releases
The new 624 area code will be an overlay to the existing 716 area code Albany, NY – July 11, 2023 – FirstLight, a leading…

FirstLight Appoints Peter Zarrella as CFO
Press Releases
Seasoned Executive brings a wealth of experience and expertise in financial management, strategic planning as well as driving empowerment at all levels of an organization…

Wirebelt Company of America Chooses FirstLight to Support its New, Energy Efficient Manufacturing Facility
Press Releases
Metal conveyor belt manufacturing company selects FirstLight for its reliable, secure, and compliant data center services, Internet and dark fiber connectivity Albany, NY – May…

A Beginner’s Guide to Disaster Recovery as a Service
Blog
In today’s connected world, downtime is not an option.

FirstLight Fiber, Inc. Names Jason Campbell as Chief Executive Officer
Press Releases
Albany, NY – April 6, 2023 – FirstLight, a leading provider of fiber-optic data, Internet, data center, cloud, unified communications, and managed services to enterprise…

FirstLight Continues Fiber Network Expansion in Hebron, Sumner
Press Releases
Rural Maine communities to benefit from high-speed Internet Albany, NY – April 4, 2023 – FirstLight, a leading provider of digital infrastructure services to enterprise…

The 2023 Hype Alphabet Soup
Blog
With 2023 in full swing, tech leaders everywhere might be feeling stretched thin. Caught between strategic activities that set the guideposts for your team and…
New 329 Area Code Coming to the 845 Region in New York
Press Releases
New assigned area codes begin March 24th, 2023 Albany, NY – February 1, 2023 – FirstLight, a leading provider of digital infrastructure services to enterprise…

FirstLight Receives 2022 Backup and Disaster Recovery Award from Cloud Computing Magazine
General News
Ransomware Protection, Data Backup and Disaster Recovery as a Service Honored for Enhancing Organizational Security Albany, NY – January 30, 2023 – FirstLight, a leading…

FirstLight Announces Expansion of Residential Broadband in Maine
Press Releases
This investment helps to bridge the digital divide in unserved and underserved areas throughout the state Albany, NY – December 7, 2022 – FirstLight, a…

Performance-Grade Ethernet Explained
General News
As enterprise leaders work to create more seamless connections among office locations, data centers and cloud applications, they are increasingly choosing private connections like Ethernet.…

The Divide Podcast: How FirstLight is connecting communities with middle-mile fiber
General News
This week: FirstLight Fiber’s Maura Mahoney, Chief Marketing Officer, and Patrick Coughlin, Chief Development Officer, talk about tackling the digital divide through fiber ‘onramps and…
FirstLight to Exceed 1,700 Route Miles in New York in 2022
Press Releases
With over twelve hundred route miles already constructed this year, FirstLight remains committed to expanding in the Empire State Albany, NY – October 25, 2022…