In the past, all you had to do was secure your perimeter and your data was safe. Technology has evolved and changed all that. Today, your data is dispersed: it’s in the cloud, in your employee’s mobile devices, and in your data center.
You have a responsibility to protect your valuable data, no matter where it resides. Hackers are out there and they are well-funded, equipped with high-tech tools, and determined to steal your data.
In the first half of 2018 alone, according to breachlevelindex.com, the total number of records compromised was 3,353,172,708 — a staggering figure that represents a 72 percent increase over the first half of 2017. Of all incidents measured, only 21 used encryption on the data (either in part or in whole). Surprisingly, this number was less than half the figure for the previous year, even though encryption is a simple way to protect your data from breaches.
Why Managed Edge Security?
 The old-school method of setting up a firewall perimeter around your local environment is not enough to ensure the safety of your business data in today’s complex technology ecosphere. To address today’s security threats, you need managed edge security. It gives you the power to encrypt your data wherever it might be: on a salesperson’s laptop, in the cloud, or in your own data center.
The old-school method of setting up a firewall perimeter around your local environment is not enough to ensure the safety of your business data in today’s complex technology ecosphere. To address today’s security threats, you need managed edge security. It gives you the power to encrypt your data wherever it might be: on a salesperson’s laptop, in the cloud, or in your own data center.
In this article, we’ll explore 3 reasons why you must have managed edge security.
Use of IoT Devices
In the span of just a few years, everything got smart. People’s cars, toasters, and stereo speakers can now connect to the cloud. This is the world of IoT devices.
In a business environment, IoT devices are used for many tasks, including product tracking, environmental monitoring, and communications. These are just a few use cases for IoT, and many more are emerging. All of these devices contain data that should be secured.
Threat of Cybercrime
The threat of cybercrime is real. Even big players like Facebook and Google have become victims. Data encryption is an easy way to secure your data. When your data is encrypted, it loses its market value for hackers. However, what makes attacks even more difficult to identify is that hackers are also using encryption to avoid detection. That’s why there’s a growing need to encrypt data both in motion and at rest to avoid even these kinds of sophisticated attacks.
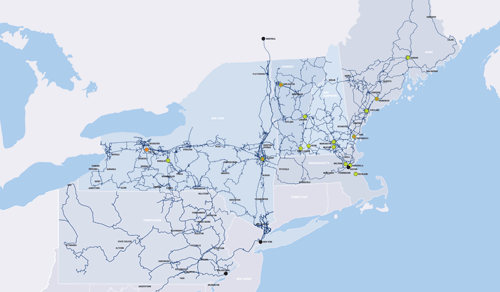
Geographically Dispersed Assets
 Technology has enabled a new kind of workplace. Teams are geographically distributed, and so is enterprise data. Many companies now store valuable data in the cloud and in edge devices such as employee mobile phones, tablets, and . All these endpoint connections create vulnerabilities that require new and more sophisticated strategies to safeguard data – namely layer 1 encryption, router safeguards, and more vigilant network monitoring.
Technology has enabled a new kind of workplace. Teams are geographically distributed, and so is enterprise data. Many companies now store valuable data in the cloud and in edge devices such as employee mobile phones, tablets, and . All these endpoint connections create vulnerabilities that require new and more sophisticated strategies to safeguard data – namely layer 1 encryption, router safeguards, and more vigilant network monitoring.
A New Way to Think About Security
With the advent of IoT and the cloud, IT professionals have to adjust their way of thinking about . The ‘always-on’ protection of a low-latency Encrypted Wavelength solution ensures that critical data is protected and secure in flight at layer 1, the transport layer.
Furthermore, rather than protecting a physical barrier, like a network or data center, IT managers need to better protect the data itself. This is where managed edge security comes in.
With a managed edge solution, you can achieve complete data visibility. Protect your data wherever it resides with encryption and access management. A managed edge security solution can help you establish complete data control with end-to-end encryption and access management tools, including secure router services and network monitoring.
If you are not sure what steps to take to implement a managed edge security solution, talk to your managed services provider. Your provider can support you with security assessments, solution design, implementation, and support.
Find out how FirstLight can optimize the protection and management of your network and free up your IT staff from maintenance and updates with its Managed Edge Routing and Security solutions. Download our Managed Edge Security and Managed Edge Routing fact sheets.