The threat landscape is constantly changing as cybercriminals adapt and seek new ways to exploit weaknesses. Cybercriminals change their attack vectors, ferreting out new vulnerabilities and tweaking malware to make it more effective.
The types of threats your company faces may be unique to you. Some businesses face more general threats, while others experience targeted attacks.
Your company can never relax its defenses. Data security is essential to protect sensitive mission-critical data, as well as the personally identifiable information of your clients and customers.
Here are 5 areas of data security your company must address to combat risk:
 1) Prepare for DDoS attacks
1) Prepare for DDoS attacks
Distributed Denial of Service (DDoS) attacks are crippling. A cybercriminal uses bots to overwhelm a company’s network with queries, making users unable to access the system and eventually causing a shutdown. DDoS attacks target an organization’s availability, which is necessary to provide a satisfying user experience and to earn the trust of customers.
Your company must always be vigilant against DDoS attacks. The FBI recently released an alert, warning that DDoS attacks may take advantage of previously undiscovered vulnerabilities that could expand the attack surface.
Your network provider can be a valuable ally before and after a DDoS attack. The right provider can work with your company to monitor the network for suspiciously heavy traffic and help to redirect traffic to avoid the network from being overburdened.
2) Focus on encryption
When data hasn’t been properly encrypted, it is useful to a hacker trying to steal identities, commit fraud, or sabotage your company. With encryption, only the authorized receiver of the data can decrypt and make use of it.
Data must be encrypted at rest, in flight, and in the cloud to be kept truly secure. Your cloud provider should be encrypting your data before it is stored in the cloud.
Typically, data is encrypted at Layer 2 or higher, but this interferes with performance when data is being transmitted. Encrypted wavelength solves performance problems by encrypting data at Layer 1, the transport level. With encrypted wavelength, data can be transmitted safely and quickly so it retains its actionable value.
 3) Ensure you have adequate backup and recovery
3) Ensure you have adequate backup and recovery
Backup and recovery is essential for bouncing back from a cyberattack, such as a ransomware attack that has locked down all your company’s files. At least one copy of your backup files should be stored off-premises to keep it from being lost or destroyed if your on-site storage is compromised. You should also have two backup copies on two different media.
Regularly testing your backup and recovery strategy increases the likelihood that it will work under real-world conditions. Testing will let you know if you can realistically meet recovery time objectives (RTOs) and recovery point objectives (RPOs). As capacity changes, backup and recovery resources need to be increased. Testing will let you know if you have met the necessary requirements.
4) Make sure your disaster recovery plan is up to date
Like your backup and recovery strategy, your disaster recovery (DR) plan can get out of date. Your DR plan should be flexible enough to protect your data and applications from a variety of threats. Take stock of your current threat landscape to determine if your DR plan is adequate. Are you prepared for a major breach, equipment failure, or natural disaster?
Your business should review its disaster recovery plan frequently. Any infrastructure changes, new applications, and additional sources of data should be accommodated by your DR strategy. Your company can also use past experience with disasters to prepare for the next traumatic incident.
 5) Take Advantage of Managed Services
5) Take Advantage of Managed Services
Your company doesn’t need to go it alone. Outsourcing data security services gives your business access to top security tools and expertise.
More than half of organizations have an outdated firewall, leaving their perimeters vulnerable.
Firewall as a service ensures that your company’s firewall is up to date and can respond to today’s threats.
Network monitoring can also be provided by a trusted third party, freeing your IT staff from the burden of 24/7 vigilance. Finding a partner with a network operations center (NOC) gives your company peace of mind. In the NOC, a full staff of security experts works tirelessly to detect, prevent, and mitigate attacks on your network.
Bridge Your Data Security Gaps
To ensure your company has a robust and comprehensive data security strategy, it helps to work with a technology partner that offers a wide range of security tools and services. This partner can collaborate with your IT team to set and meet data security goals and future-proof your strategy.
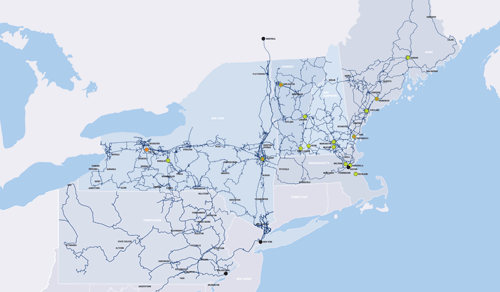
FirstLight is an ideal data security partner for organizations in the Northeast and mid-Atlantic. We are more than a managed security services provider. We own and operate our data center, network, and cloud resources. We partner with Cisco to deliver firewall and network security. We also provide encrypted wavelength, backup and recovery, and disaster recovery as a service.
Find out more about what FirstLight can do to help your company beef up its security strategy. Reach out to us today.