Security strategies need continual enhancement. Hackers are tireless in their quest to find new ways to overcome your company’s defenses. Cybercriminals are always changing attack vectors and adapting the tools they use to infiltrate your systems and steal your data.
The first step in developing a timely security strategy is assessing the nature and level of risk to which your company is being exposed. Once you have identified your vulnerabilities, you can develop a road map to build a new, more effective security solution.
Here is a look at 5 steps in a security risk assessment:
1.) Gain visibility into all assets.
If you don’t know you own something, you can’t protect it. Assets can be difficult to track and monitor when they come from multiple vendors and have been implemented across the business.
Shadow IT has compounded the problem of visibility. Line of business employees have become increasingly comfortable with implementing technology without going through the IT department. These services may expose your company to potential threats without you even knowing it.
2.) Confirm due diligence of all vendors.
Every vendor offers its own service level agreement (SLAs) associated with the services or products it provides to your company,. You should understand those protections offered by the SLAS and hold these vendors accountable for the security of its solution, but to what degree? You don’t want to drop the ball on an aspect of security because you mistakenly thought the vendor was handling it.
When companies work with an outsourced IT provider, it may not be clear what security responsibilities the vendor has. It may be necessary to monitor the vendor to ensure it is meeting required standards of data privacy and protection.
3.) Conduct in-house vulnerability testing.
Wolf & Company’s risk management experts found that known, unpatched vulnerabilities are the cause of 44% of data breaches. Companies often fall behind on security patches or fail to upgrade and refresh hardware and software when they reach end of life. Hackers use tools to scan your systems for vulnerabilities that they can use to attack your company.
A thorough risk assessment should include a scan of all company assets to pinpoint vulnerabilities. Your company should leverage patch management to prevent hackers from using exploit kits to infiltrate your business. Working with a provider that offers infrastructure as a service (IaaS) can help too, by keeping core systems patched and up-to-date while your internal IT staff can focus on specific applications and data.
4.) Evaluate access control and authentication.
Hackers often use social engineering to fool employees into giving out access information. They send phishing emails that seem to come from trusted companies or executives at your business. Even without social engineering, many cybercriminals can use encryption tools to uncover passwords.
Companies should evaluate their authentication methods. If your business is relying on a single or double-factor authentication system, you should consider a multifactor approach. Multifactor authentication often uses biometrics such as fingerprint or retinal scans to stop imposters in their tracks.
Your company may also want to reevaluate the level of access you grant to employees. Consider what information an employee needs to do his or her job effectively.
5) Understand the threat landscape.
You can’t properly defend your business unless you can adapt your security strategy to potential threats.For insance, if you’re prepared for an exploit but unprepared for the ransomware attacks popular with hackers, you’re out of luck. Your company should keep track of current and emerging threat trends.
Your organization needs to be aware of how cyberattacks are evolving and what attack vectors hackers are using. Information about the threat landscape gathered from dashboards or reports by security experts empowers you to adapt your security strategy to prevent breaches.
Planning for Better Security
Third party organizations can provide unbiased security assessments and recommendations that will pointpoint vulnerabilities and show areas that need improvement. Companies like FirstLight can be part of an overall approach to improving security as well, with solutions such as secure colocation, managed firewalls, cloud-based disaster recovery and infrastructure as a service.
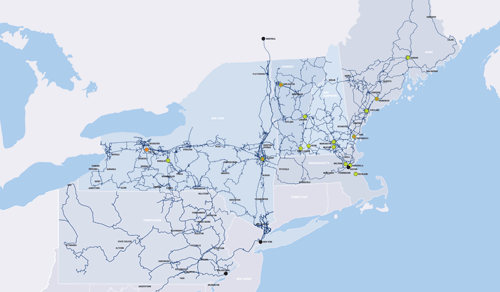
FirstLight has a long track record of working with companies that have high risk profiles. We have helped many companies including those in the fields of finance, health care, and education develop effective security strategies. Our colocation and cloud solutions provide multiple layers of security to guard against data loss or compromise. Our extensive fiber optic network coupled with our secure cloud, data center, colocation and as-a-service offerings will keep your data safe and sound.
Reduce your level of risk. Work with FirstLight on a new disaster recovery strategy.