The distributed denial of service (DDoS) attack staged by the Mirai botnet in the fall of 2016 is legendary for its scale and reach. Hackers managed to weaponize thousands of unsecured IoT devices. The botnet was then used to flood the internet with traffic, crippling large businesses all over the world, including Dyn, a company that hosts domain name systems (DNS) for major websites.
When reporting on a more recent DDoS attack, Dark Reading noted that these attacks are becoming more difficult to fight because they are growing in speed and intensity and use multiple source addresses and ports.
Your company may feel it is doing enough to protect itself against a DDoS attack, but is it?
Even if you are using a firewall with an intrusion detection system (IDS) and intrusion prevention system (IPS), you still may not be doing enough to stop a DDoS attack. Fighting a DDoS attack with a firewall may actually make your organization more vulnerable or disrupt your business further.
The Downside to Firewalls
 Firewalls may seem to be an ideal defense against DDoS attacks. After all, firewalls are designed to keep suspicious network traffic from breaching the perimeter of company systems. The firewall filters incoming packets of information, checking to see if they meet specific criteria before allowing them through. However, when confronted with excessive traffic, the firewall may slow the transmission process down even further, leading to disruptive downtime.
Firewalls may seem to be an ideal defense against DDoS attacks. After all, firewalls are designed to keep suspicious network traffic from breaching the perimeter of company systems. The firewall filters incoming packets of information, checking to see if they meet specific criteria before allowing them through. However, when confronted with excessive traffic, the firewall may slow the transmission process down even further, leading to disruptive downtime.
Firewalls may even serve as entry points for DDoS attacks. The firewall ports that are intended to allow authorized traffic to enter may enable DDoS traffic to slip through.
Hackers also stage DDoS attacks by creating thousands of fake IP sender addresses, making it difficult to identify the location of the attacking machines. These fake addresses sometimes come off as legitimate addresses, fooling the firewall.
Companies that want to protect themselves against DDoS attacks need a defense measure that will stop the attack before it reaches the perimeter.
The Limits of an Intrusion Detection System (IDS)
As the name suggests, an IDS detects anomalous traffic that may signal a threat. The IDS can then record and report the anomaly. However, the IDS does nothing to stop the threat.
In the case of a DDoS attack, the IDS may go into overdrive detecting malicious traffic. However, it won’t stop this traffic from crippling your company’s network and blocking legitimate users from conducting business. Unless the same type of DDoS attack strikes your company again, the information gathered does no good to protect you in the future.
An Ounce of Intrusion Prevention
 What about an intrusion prevention system (IPS)? Unlike the IDS, the IPS both detects the potentially malicious activity and prevents it from breaching the perimeter. This sounds perfect, right?
What about an intrusion prevention system (IPS)? Unlike the IDS, the IPS both detects the potentially malicious activity and prevents it from breaching the perimeter. This sounds perfect, right?
Not so fast. The IPS wasn’t designed to protect against DDoS attacks. The IPS detects and prevents a single attempt of an intrusion at a time. An IPS is no match for thousands of attempts made by the zombie minions involved in a DDoS attack.
Finding a Solution Designed to Fight DDoS
There’s nothing wrong with firewalls, IDS, and IPS. These solutions perform their intended tasks effectively, preventing typical attempts at a breach and maintaining records of malicious signatures to prevent future attacks. However, DDoS attacks require special attention.
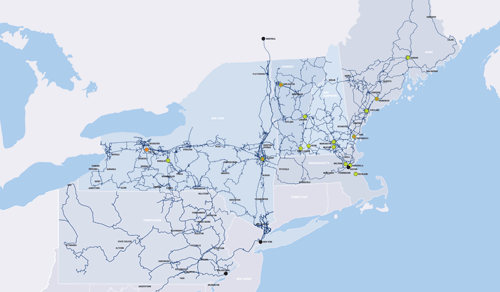
As part of FirstLight Internet Services, we offer DDoS Protection and Mitigation that takes a preventive approach to fighting DDoS attacks. We monitor your network traffic 24/7, using sophisticated algorithms to detect potentially malicious traffic, including new and emerging threats. Our mitigation process lessens the impact of DDoS traffic, allowing legitimate traffic to proceed uninterrupted.
Find out more about FirstLight DDoS Protection and Mitigation. Reach out to us today.