While higher education institutions may not seem like typical targets for cybercriminals, colleges and universities hold a treasure trove of valuable information.
Colleges and universities handle the personal and financial information of their students, making campuses ripe pickings for identity theft. Research universities conduct studies and innovate, producing valuable intellectual property. Between the labs, classrooms, administrators and students, there are so many connected devices that malware and scams can spread like wildfire.
So, how did this all come to be?
The Security Challenges Facing Higher Education
 Higher education has a tricky relationship with cybersecurity that boils down to a fundamental difference in philosophy. Colleges and universities promote collaborative principles and the open exchange of information. They’re about making connections and breaking down the barriers between communication and understanding.
Higher education has a tricky relationship with cybersecurity that boils down to a fundamental difference in philosophy. Colleges and universities promote collaborative principles and the open exchange of information. They’re about making connections and breaking down the barriers between communication and understanding.
Cybersecurity is about putting up barriers, walls and gateways, and keeping information guarded to avoid getting into the wrong hands.
So how can these two opposed philosophies co-exist, especially when 48% of IT administrators at higher education institutions believe that the greatest security risks come from within the campus?
To be successful, the network security solution must address the four biggest challenges for data security in higher education.
- User-Generated Vulnerabilities
What’s common on every college campus? Public Wi-Fi and hundreds of thousands of edge devices. A recent survey revealed that 60 percent of faculty, students, and IT professionals at a typical university use four or more devices on the campus network.
On the public network, there’s sensitive data being attached to emails with little to no encryption, and users are creating weak passwords. Given the number of information exchanges happening on just one regular weekday, it’s easy to see how user-generated vulnerabilities quickly multiply to create a cybersecurity disaster.
- Multiple Silos
Universities aren’t a single entity. They’re made up of multiple organizations that have their own security concerns. A student health center will have to adhere to HIPAA. Departments that process credit card payments must be PCI compliant. The campus police need to be CJIS compliant.
The difference in security needs can be so great between these entities that having an all-encompassing compliance policy is near impossible; therefore, each department must self-govern its own requirements. This creates silos and a breakdown in standards between entities and departments. All this discord creates cracks in the overall campus security infrastructure.
- Inertia
Sometimes, when a challenge seems insurmountable, it continues to be put on the back burner. Overhauling a college’s or university’s network security is a long-term project that, with all the existing silos, no one wants to tackle.
The longer it’s put off, the harder it becomes. What happens, then, is that organizations within the campus start implementing their own systems, leading to a lack of coherency that further erodes open communication and the sharing of ideas.
- Lack of Resources
IT departments on campuses are often fragmented between organizations under the college or university umbrella. Talent shortages are not uncommon. With the long-term nature of a sweeping network overhaul, expenses can rise quickly. It can be very difficult to obtain approval for funding. Consequently, changes to network security often wind up being short-term patches rather than sweeping reform.
The Need for Cloud-Based Edge Security
 With edge security, colleges and universities have a solution to their cybersecurity problems. With encrypted VPN connections and meshed VPN as an all-encompassing security overlay over the campus, data shared between edge devices and various campus networks are now protected.
With edge security, colleges and universities have a solution to their cybersecurity problems. With encrypted VPN connections and meshed VPN as an all-encompassing security overlay over the campus, data shared between edge devices and various campus networks are now protected.
SD-WAN allows for encrypted “tunnels” to be created and terminated between different networks, so all existing campus silos can now be safely connected to each other and the central college network, helping to keep with the tenets of collaboration and the free flow of information.
With encrypted waves, network monitoring, specialized routers, and multiplexers, data is also analyzed at the edge for security threats, instead of solely at the network center. This means that the response to security threats and events happens in real time.
Edge Security Protection for Colleges and Universities
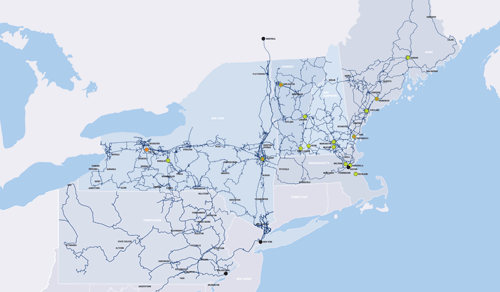
FirstLight offers a free consultation to higher education institutions so they can discover how a cloud-based edge security solution can protect data while still allowing for the free flow of information.
Download our Managed Edge solution fact sheet. Contact us today to bring data security to your university or college campus.