Cybercriminals are continually adapting their strategies to avoid detection and overcome traditional defenses. Each time a new technology is developed, hackers quickly zero in on its vulnerabilities. Bad actors are always innovating and inventing unique attack vectors.
As security threats become increasingly sophisticated, companies have a hard time staying ahead. Awareness is part of the solution. Organizations need to stay informed about the current threat landscape so they can adapt their security strategies.
Here is a look at 3 security threat trends that your business should know about:
1) New ransomware attack vectors

Ransomware has become one of the most popular methods of attack for cybercriminals. They use emails with infected attachments to encrypt essential files and bring companies to their knees. The hackers demand a ransom in cryptocurrency in exchange for a decryption key.
Ransomware is also notorious for evolving to employ new attack vectors. More recent attacks have been executed by scanning public IP addresses for vulnerable remote desktop protocol (RDP) servers. This method bypasses phishing emails entirely. Some new strains of ransomware automatically delete on-site backup files.
Companies need to leverage cloud providers to help protect against ransomware. The cloud offers replication and a separate environment that allows you to roll back the clock to before the ransomware took hold.
2) Weaponization of IoT
As the internet of things (IoT) is becoming more prominent, it has created new opportunities for hackers to breach or disable company systems. In IoT, every connected device is an endpoint that can be used to infiltrate the perimeter. When data is transmitted from the device to the cloud or primary data center, information is exposed, which makes it vulnerable to being stolen or compromised in transit.
Not only does IoT create new points of vulnerability, it can also be turned against a company. Hackers can infect the IP addresses of connected devices, turning them into botnets. These botnets can then be used to attack the company that owns the devices, or other companies.
Recently, botnets created from IoT devices have been used to stage massive distributed denial of service (DDoS) attacks. The botnets inundate networks with traffic, crashing a company’s system and preventing legitimate users from gaining access.
In December 2017, the U.S. Department of Justice announced that it had brought charges against the hackers responsible for the Mirai botnet attacks that occurred the previous year. The defendants were able to infect hundreds of thousands of IoT devices
3) Cybercrime as a Service

Aspiring cybercriminals don’t need to understand code or master software development to hack into a company’s systems. Malware, ransomware, exploit, or trojan toolkits can be purchased on the dark web for as little as $100.
According to The Criminal Cyberservices Market 2018 report, tools for attacking ATMs can be purchased for around $1,500, giving criminals access to hundreds of thousands of dollars in one machine. Alarmingly, the report shows that the demand for the development of cybercrime services exceeds the supply by a factor of 3, showing that this trend won’t be slowing down anytime soon.
Staying Ahead of Emerging Threats
The cyberthreat landscape is frightening, but your company doesn’t need to feel overwhelmed. Every attack vector has a defense. Anticipating threats and being proactive about security helps your company stay ahead.
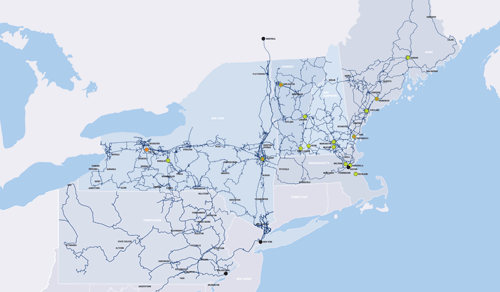
At FirstLight, every solution we provide takes security into account. Our fiber optic network offers security and resilience that is superior to that provided by traditional copper cables.
Our cloud services include disaster recovery as a service. By providing cloud services supported by a fast and powerful network, we give your business a better chance of standing up to a DDoS attack.
We also provide the option of ultra-secure colocations for your data center. All of our data centers offer physical and virtual security, including 24×7 monitoring. Our Romulus, New York, data center is housed in a former military installation, for ultimate peace of mind.
Find out more about how the right technology partner can defend your company against emerging cyberthreats. Reach out to FirstLight.