In July, the finance world was rocked by the news of a large breach at a major financial services company. A single hacker stole enormous amounts of data from its customers, and the New York Attorney General quickly started an investigation into whether this finance industry behemoth was negligent in its security.
It’s a given that the company’s edge security measures will be under high scrutiny.
Why? Edge security just so happens to be the much-needed future of security, particularly in the financial world.
 What Is Edge Security?
What Is Edge Security?
Before smartphones and the explosion of IoT devices, corporate Internet security was a fairly simple affair. A company’s Internet security basically put a bubble around the server and storage. Data collected was scanned and analyzed once it entered the bubble.
Web browsers and browser add-ons were the means of access and interface, and among the biggest concerns were computer worms. While these worms were nasty, much worse was on the horizon.
As The Washington Post points out, 2003 was the year that security concerns really started to escalate. In this year alone, the amount of data created over the Internet surpassed all the information created in the entirety of human history, and with more devices accessing the Internet, the potential entry points for attacks increased substantially.
Then came smartphones, followed by the proliferation of IoT devices.
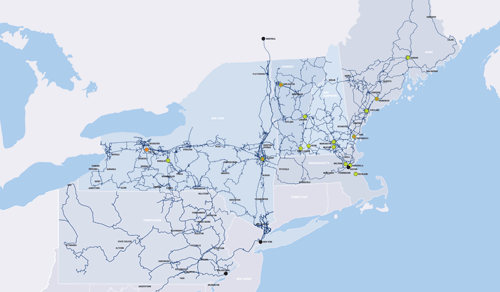
With billions of devices communicating with each other all around the world, company and client data must be protected from every device on or circling our planet.
That’s edge security.
Edge Protection
Along with government entities, the finance industry is at the top of the list for criminal attacks. From DDoS and ransomware to sophisticated data breach attacks, hackers want information they can profit from. What’s more profitable than account numbers and personally identifiable information?
According to techjury, mobile devices had a 2018 worldwide market share of 52.1% while the market share for desktop devices was 44.2%. Additionally, mobile devices were estimated to account for nearly 80% of 2018 Internet usage.
Whether app payments, banking, or online shopping, money being shifted across mobile devices is rapidly on the rise. All companies, including finance, have to protect their customers’ information, as data leaks are now almost a daily occurrence.
With edge security, financial companies enable users to share their private data while having control over what data is stored in a company’s system. Data is encrypted on user devices before being sent to the corporation for storage. There are a number of technologies in effect to accomplish this goal.
1: Encrypted VPN (Virtual Private Network)
Smartphones are edge devices, as are sensors, smart appliances, and any device that is Wi-Fi enabled. With an encrypted VPN connection between an edge device and a business’s network, only computers with the right decoder can read and use the data being transmitted, thus limiting the line of transfer to the end user and the company server.
2: Meshed VPN
IoT devices don’t work solely in a silo. They can connect with any other designated IoT device throughout the whole system. Meshed VPN acts as a security overlay for IoT devices to interact with each other over public networks, whether that’s mobile data or the guest network at area businesses.
3: Data Is Now Analyzed at the Edge
With the proliferation of public networks, it’s essential to bring security all the way down to the initial entry points of a business’s network. With the increased sophistication of edge devices, such as specialized routers and multiplexers, it’s now possible to both analyze data at the edge for security threats and respond to any threats or events in real time.
Additionally, segmentation and micro-segmentation can be performed at the edge to assign an edge device to a specific network segment.
4: SD-WAN (Software-designed Wide Area Network)
Along with increased network agility, SD-WAN allows for the creation and termination of encrypted “tunnels” between different networks. This is especially helpful for connecting multiple branch offices to the main corporate server.
5: NAC (Network Access Control)
NAC provides the ability to control the behavior of any device connecting to the main network. It identifies the connected device and sets the policy for how that device can interact with the main server. It also provides control over applications that are attempting to connect to the main server, whether it’s an internal or external device.
 How Will Your Financial Institution Benefit from Edge Security?
How Will Your Financial Institution Benefit from Edge Security?
As mentioned earlier, cyberattacks and hacking will only continue to become more prevalent. Consumers need the peace of mind that the financial information they provide is safely stored and sheltered from prying eyes.
Consumer confidence in a company can erode quickly when private information is stolen. This makes edge security no longer an option, but a must.
Download our Managed Edge fact sheet today. Contact FirstLight today for a free consultation on how our edge security solutions will beef up IoT and network protection while bolstering consumer confidence in your brand.