Your company’s network is like its circulatory system. Data flows through the network giving life to all aspects of your business.
The network is vital to your company’s health, so you can’t afford to let it be compromised. Malware can infect your systems through the network. Hackers can use the network as a conduit to infiltrate your business and steal valuable data. Almost everyone is a target, not only for the valuable data on your business’ network, but because your network can be used as a launch point to infiltrate the networks of your customers and partners.
As organizations rely on more endpoints for gathering data and interacting with third parties, protecting the edge of the network has become increasingly important. The more endpoints a company has, the larger the network becomes, and the more vulnerable to network intrusions it becomes as your attack surface widens.
Let’s take a look at 5 factors that make network edge protection crucial for your business:
1) Ransomware attacks using routers
 Originally ransomware attacks were committed using a standard attack vector. Hackers used phishing emails to trick employees into opening an infected attachment that would encrypt all the company’s files. Victims were asked for a ransom in return for a decryption key.
Originally ransomware attacks were committed using a standard attack vector. Hackers used phishing emails to trick employees into opening an infected attachment that would encrypt all the company’s files. Victims were asked for a ransom in return for a decryption key.
Today, cybercriminals are bypassing the phishing email and using network routers to gain access to company systems. These attacks are more aggressive than earlier forms of ransomware because they automatically delete on-site backup files.
2) DDoS attacks
Distributed denial of service (DDoS) attacks highlight two vulnerabilities in the traditional network: ungated access and intolerance for overload. DDoS attacks overwhelm the capacity of the network by bombarding it with queries. The increased network traffic prevents legitimate users from conducting business on the network.
DDoS attacks are also often committed by botnets that have been created by infecting devices through vulnerable routers. IoT devices are particularly vulnerable because they typically are not designed with security in mind. In 2016, Mirai botnet attacks used weaponized IoT devices to paralyze businesses around the world.
3) Zero-day exploits
 Zero day exploits are aptly named because when discovered, they are considered day zero – that is, no days since discovery. Zero-day exploits take advantage of bugs in newly developed software or hardware. The Ponemon Institute’s 2018 State of Endpoint Security Risk Report found that 64% of the organizations surveyed had experienced a zero-day exploit attack in the previous 12 months.
Zero day exploits are aptly named because when discovered, they are considered day zero – that is, no days since discovery. Zero-day exploits take advantage of bugs in newly developed software or hardware. The Ponemon Institute’s 2018 State of Endpoint Security Risk Report found that 64% of the organizations surveyed had experienced a zero-day exploit attack in the previous 12 months.
These applications are often run at endpoints that provide a point of entry for the hacker to infiltrate an entire system through the network. According to the Ponemon report, a patch can take an average of 102 days to be applied, giving hackers plenty of time to wreak havoc.
4) Rise of the internet of things (IoT)
IoT consists of connected devices equipped with sensors that generate data. Each one of these devices is now an endpoint connected to the network, which has exponentially increased the number of access points and thus made networks more vulnerable.
As in the case of the Mirai botnet, IoT devices can be weaponized by cybercriminals. They also provide thousands of points of entry for hackers who want to infiltrate your company’s network. Hackers could even hijack your IoT sensors, causing vital assets to go haywire.
5) Risks of third-party applications
 Third-party applications provide another point of vulnerability for companies. When third-party applications are installed, the user seldom changes the default passwords, making the software easy to hack into.
Third-party applications provide another point of vulnerability for companies. When third-party applications are installed, the user seldom changes the default passwords, making the software easy to hack into.
Third-party applications are often customer-facing and present a tempting target for hackers who want to steal personally identifiable or financial information. Many hacks are accomplished through point-of-sale systems that use third-party software.
How to Protect the Network Edge
Now that you’ve explored some of the risks at the network edge, what should you do about it?
The amount and variety of edge devices that companies use makes protecting the network edge challenging. Firewalls can prevent attacks from breaching the perimeter, but monitoring the network is the key to building a layered defense that gets closer to the origin of the problem.
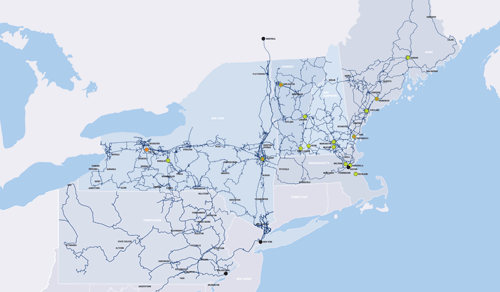
FirstLight’s Managed Edge Security solution provides customers with next-generation firewall services and unified threat mitigation to protect their network.
Does your company have confidence in its network? Learn more about FirstLight’s Managed Edge solutions. Let FirstLight give you peace of mind.